Darktrace Resources
Grazie! Il vostro invio è stato ricevuto!
Risorse
Gated Video

NIS2 Directive: Implications on Cyber Security and AI
Gated Video

NIS2 Directive: Implications on Cyber Security and AI
Risorse
April 16, 2024
services,managed,detect,respond
4
Scheda tecnica

Darktrace Services: Managed Detect + Respond (MDR)
4
services,managed,detect,respond
Scheda tecnica

Darktrace Services: Managed Detect + Respond (MDR)
Risorse
April 9, 2024
Scheda tecnica

State of AI Cyber Security 2024 Infographic
Scheda tecnica

State of AI Cyber Security 2024 Infographic
Risorse
December 12, 2023
Gated Video

BSI Lagebericht 2023 Webinar 🇩🇪
Gated Video

BSI Lagebericht 2023 Webinar 🇩🇪
Risorse
February 22, 2024
3
Gated Video

Exploring the Evolving Email Security Landscape
3
Gated Video

Exploring the Evolving Email Security Landscape
Risorse
April 9, 2024
Scheda tecnica

State of AI Cyber Security 2024 Executive Summary
Scheda tecnica

State of AI Cyber Security 2024 Executive Summary
Risorse
March 26, 2024
3
Gated Video

Darktrace/Cloud Product Spotlight
3
Gated Video

Darktrace/Cloud Product Spotlight
Risorse
April 9, 2024
2
Libro bianco

State of AI Cyber Security 2024
2
Libro bianco

State of AI Cyber Security 2024
Risorse
April 10, 2024
platform, email, OT, Virtual Innovation Launch
2
Video
Darktrace Virtual Innovation Launch
2
platform, email, OT, Virtual Innovation Launch
Video

Darktrace Virtual Innovation Launch
Risorse
April 9, 2024
platform
2
Scheda tecnica
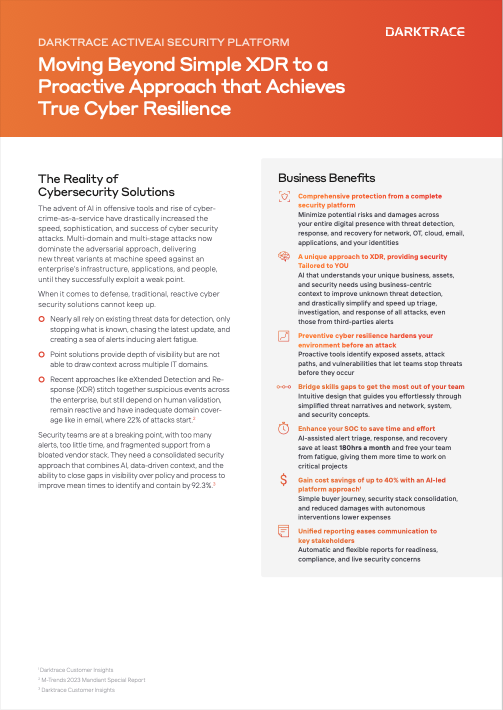
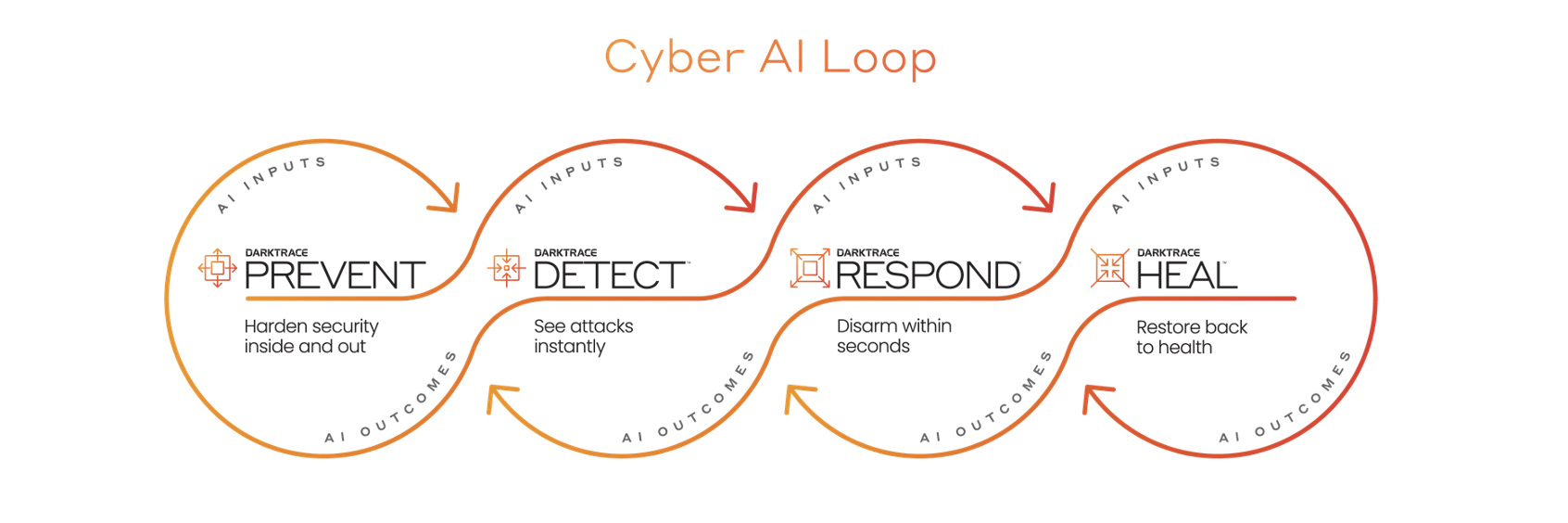
Darktrace ActiveAI Security Platform Solution Brief
2
platform
Scheda tecnica

Darktrace ActiveAI Security Platform Solution Brief
Risorse
April 9, 2024
OT,Darktrace/OT Solution Brief,ICS
3
Scheda tecnica

Darktrace/OT Solution Brief
3
OT,Darktrace/OT Solution Brief,ICS
Scheda tecnica

Darktrace/OT Solution Brief
Risorse
April 9, 2024
email
3
Scheda tecnica
Darktrace/Email Solution Brief
3
email
Scheda tecnica

Darktrace/Email Solution Brief
Risorse
March 28, 2024
5
Video
Threat Analysis Stories: Detecting Exploitations of the Ivanti Vulnerability
5
Video

Threat Analysis Stories: Detecting Exploitations of the Ivanti Vulnerability
Risorse
center for internet security the 18 critical security controls
Scheda tecnica

Center for Internet Security: The 18 Critical Security Controls
center for internet security the 18 critical security controls
Scheda tecnica

Center for Internet Security: The 18 Critical Security Controls
Risorse
March 15, 2024
2023 sec cybersecurity reporting requirements
Scheda tecnica
2023 SEC Cybersecurity Reporting Requirements
2023 sec cybersecurity reporting requirements
Scheda tecnica

2023 SEC Cybersecurity Reporting Requirements
Risorse
March 7, 2024
5
Video
Threat Analysis Stories: Defending Against a Gootloader Malware Attack
5
Video

Threat Analysis Stories: Defending Against a Gootloader Malware Attack
Risorse
March 1, 2024
5
Video
Threat Analysis Stories: Catching an Attempted Dropbox Account Takeover
5
Video

Threat Analysis Stories: Catching an Attempted Dropbox Account Takeover
Risorse
March 5, 2024
Reversing the Tide: Preventing the Top 4 Supply Chain Risks in 2024,cloud,network,email,zero trust,zero-trust,prevent,detect,respond,asm,apm,supply,chain,supply chain,supply chain attacks,
4
Libro bianco

Reversing the Tide: Preventing the Top 4 Supply Chain Risks in 2024
4
Reversing the Tide: Preventing the Top 4 Supply Chain Risks in 2024,cloud,network,email,zero trust,zero-trust,prevent,detect,respond,asm,apm,supply,chain,supply chain,supply chain attacks,
Libro bianco

Reversing the Tide: Preventing the Top 4 Supply Chain Risks in 2024
Risorse
March 4, 2024
ot,Darktrace+XageJointSolution
Scheda tecnica

Darktrace + Xage Joint Solution
ot,Darktrace+XageJointSolution
Scheda tecnica

Darktrace + Xage Joint Solution
Risorse
February 29, 2024
ciso,stories,cloud,security
Libro bianco

CISO Stories: Cloud Security
ciso,stories,cloud,security
Libro bianco

CISO Stories: Cloud Security
Risorse
February 29, 2024
AI,arms,race,ciso,stories
Libro bianco
CISO Stories: The AI Arms Race
AI,arms,race,ciso,stories
Libro bianco

CISO Stories: The AI Arms Race
Risorse
February 22, 2024
trends,analysis,year,end,threat,report,pattern,intelligence,
5
Libro bianco
End of Year Threat Report
5
trends,analysis,year,end,threat,report,pattern,intelligence,
Libro bianco

End of Year Threat Report
Risorse
February 15, 2024
psychology,confirmation bias,trust,stress
4
Libro bianco
AI with Humans in Mind
4
psychology,confirmation bias,trust,stress
Libro bianco

AI with Humans in Mind
Risorse
February 15, 2024
security practices,implementing ai,LLM,gen ai,generative ai,ai adoption,reliable ai,
4
Libro bianco

Best Security Practices for Implementing AI in the Enterprise
4
security practices,implementing ai,LLM,gen ai,generative ai,ai adoption,reliable ai,
Libro bianco

Best Security Practices for Implementing AI in the Enterprise
Risorse
February 13, 2024
ot,asset,identification,ICS
Scheda tecnica

Darktrace/OT: Asset Identification for ICS
ot,asset,identification,ICS
Scheda tecnica

Darktrace/OT: Asset Identification for ICS
Risorse
February 8, 2024
FERC,order,887,support,darktrace,ot
Scheda tecnica
Darktrace in Support of FERC Order 887
FERC,order,887,support,darktrace,ot
Scheda tecnica

Darktrace in Support of FERC Order 887
Risorse
February 8, 2024
ot,integrations,digital,systems
Scheda tecnica
Darktrace/OT: Plugging into your Digital Systems
ot,integrations,digital,systems
Scheda tecnica

Darktrace/OT: Plugging into your Digital Systems
Risorse
February 5, 2024
compliance,
Libro bianco
7 Steps to Get Ahead with NIS2
compliance,
Libro bianco

7 Steps to Get Ahead with NIS2
customer story


The Museum of Flight
Si tratta di un testo all'interno di un blocco div.
museum of flight,network,email,apps,saas,endpoint,prevent,asm,attack surface management,heal,supply chain attacks,ip,data loss,attack simulation,playbook,play book
customer story


D24
Si tratta di un testo all'interno di un blocco div.
d24,directa24,cloud,email,network,apps,saas,zero trust,payment card industry data security standard,PCI DSS,compliance
customer story


Digimax
Si tratta di un testo all'interno di un blocco div.
network,email,apps,insurance
10
customer story


Abdullah Al Othaim Investment
Si tratta di un testo all'interno di un blocco div.
AOIC,othaim
customer story
.jpg)

Australian Grand Prix
Si tratta di un testo all'interno di un blocco div.
australian,grand,prix,gp
customer story


Telenor IoT
Si tratta di un testo all'interno di un blocco div.
cloud,detect,cloud-transformation,technology
10
customer story


Dreamworld
Si tratta di un testo all'interno di un blocco div.
hospitality,apps-microsoft-365,cloud-transformation,endpoint,cloud,detect,respond
10
customer story


Masonicare
Si tratta di un testo all'interno di un blocco div.
healthcare-and-pharma,detect,respond
10
customer story


Primaflor
Si tratta di un testo all'interno di un blocco div.
email,apps-microsoft-365,network,detect,respond
10
customer story


Direct Federal Credit Union
Si tratta di un testo all'interno di un blocco div.
financial-services
10
customer story


Ongweoweh
Si tratta di un testo all'interno di un blocco div.
manufacturing-and-supply
10
customer story


American Kidney Fund
Si tratta di un testo all'interno di un blocco div.
phishing,healthcare-and-pharma,cloud-transformation,nonprofit
10
customer story


Blue Bird Group
Si tratta di un testo all'interno di un blocco div.
phishing,transportation
10
customer story


Sir Robert McAlpine
Si tratta di un testo all'interno di un blocco div.
phishing,engineering
10
customer story


Differentia Consulting Case Study
Si tratta di un testo all'interno di un blocco div.
technology,apps,cloud-transformation,respond
10
customer story

Duferco Case Study
Si tratta di un testo all'interno di un blocco div.
ransomware,network,manufacturing-and-supply,respond
10
customer story


KTR Systems Case Study
Si tratta di un testo all'interno di un blocco div.
manufacturing-and-supply,respond,ransomware,phishing,network
10
customer story


City of Tyler Case Study
Si tratta di un testo all'interno di un blocco div.
phishing,work-from-home,network,account-takeover
10
customer story


Grupo Mexicano de Seguros Case Study
Si tratta di un testo all'interno di un blocco div.
government-regulations-compliance,financial-services,network,respond
10
customer story


Calligo Case Study
Si tratta di un testo all'interno di un blocco div.
phishing,vendor-email-compromise,email
10
customer story

International Baccalaureate Case Study
Si tratta di un testo all'interno di un blocco div.
education,ransomware,risk-compliance,respond
10
customer story


Funding Circle Case Study
Si tratta di un testo all'interno di un blocco div.
detect,cloud,cloud-transformation
10
customer story


Boardriders Case Study
Si tratta di un testo all'interno di un blocco div.
microsoft,network,apps-microsoft-365,respond
10
customer story


Mainstream Renewable Power Case Study
Si tratta di un testo all'interno di un blocco div.
cloud-transformation,respond,utilities,microsoft,network
10
customer story


Guardsman Group Case Study
Si tratta di un testo all'interno di un blocco div.
phishing,technology,respond
10
customer story

Copperbelt Energy Corporation Case Study
Si tratta di un testo all'interno di un blocco div.
it-ot-convergence,respond
10
customer story


Scope Markets Case Study
Si tratta di un testo all'interno di un blocco div.
network,cloud-transformation,respond,endpoint,financial-services
10
customer story

City of College Station Utilities Case Study
Si tratta di un testo all'interno di un blocco div.
ot,security-awareness
10
customer story


IVAR Case Study
Si tratta di un testo all'interno di un blocco div.
network,it-ot-convergence,manufacturing-and-supply
10
customer story


Vermaat Case Study
Si tratta di un testo all'interno di un blocco div.
microsoft,respond
10
customer story


EV Group Case Study
Si tratta di un testo all'interno di un blocco div.
network,manufacturing-and-supply,respond
10
customer story


Girton Grammar School Case Study
Si tratta di un testo all'interno di un blocco div.
education,work-from-home,network
10
customer story


CordenPharma Case Study
Si tratta di un testo all'interno di un blocco div.
healthcare-and-pharma,respond,data-protection,network,malicious-crypto-mining
10
customer story


City of Las Vegas Case Study
Si tratta di un testo all'interno di un blocco div.
government-and-defense,respond,heal,apps,phishing,network
2
customer story


Sanabel Al-Salam Case Study
Si tratta di un testo all'interno di un blocco div.
supply-chain-attack,phishing,respond
10
customer story

Greater Omaha Packing Case Study
Si tratta di un testo all'interno di un blocco div.
manufacturing-and-supply,respond
10
customer story


Bank One Case Study
Si tratta di un testo all'interno di un blocco div.
phishing,vendor-email-compromise,email,supply-chain-attack
10
customer story


AAA Washington Case Study
Si tratta di un testo all'interno di un blocco div.
cloud-transformation,respond,endpoint,apps,microsoft,network,security-awareness
10






































.jpg)








_11zon.jpg)













.jpeg)






















.jpeg)

%20copy.png)